Scaling Success: Secure Remote Access and Scalability in Contact Centers
The shift to remote work has transformed how contact centers operate. Ensuring secure remote access and scalable solutions are essential
Our hand-picked technology partners amplify our ability to architect and implement multi-vendor solutions, enabling seamless, secure, and efficient integration of cloud and next-generation networks into a single easy-to-manage solution.
Featured Partners
Gain invaluable customer insights to provide personalized experiences your customers want.
Enhance your data security and network connectivity with our trusted team of experts, available 24/7.
Move your manufacturing business forward with expert custom solutions and optimized applications.
Innovative solutions keep security, budget and enhanced experiences top of mind.
Seamlessly transition to most up-to-date technology while keeping your patients’ health data safe.
The shift to remote work has transformed how contact centers operate. Ensuring secure remote access and scalable solutions are essential
Contact centers handle vast amounts of personal and financial sensitive data, making robust security measures and compliance with regulatory standards
Operational excellence is not just a goal—it’s a necessity. Efficient network management lies at the heart of Lightstream’s endeavor, ensuring
Are you tired of navigating the maze of networking and security solutions? Picture this: a single platform that seamlessly integrates
Maximizing Business Potential and Cutting Costs In our previous installment, we dissected the inefficiencies of Plain Old Telephone Service (POTS)



A recent survey by Qualys and published in SC Magazine suggests that after over 3 months, millions of Log4j vulnerable systems still unpatched, roughly 1 in 3 devices and installations that were affected by the Log4j vulnerability are still unpatched. This number amounts to roughly 22 million vulnerable application installations — and it should be noted that these are just the devices that are readily accessible from the Internet.
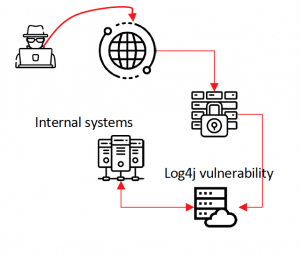
Log4j reached critical status towards the end of 2021 when it was discovered that a feature its platform could allow an unauthenticated attacker to take complete control over a remote system. The vulnerability was classified in CVE-2021-44228, and has been extensively discussed in cyber security as well as in a published flash with guidance from the government’s cyber security agency, CISA, who published guidance.
Business Impact
This Log4Shell vulnerability, as it’s been colloquially named, impacts business systems exposed to the Internet (and systems connected to them) and can result in compromise of system and data integrity, as well as complete take-over of a system or platform generating severe operational and financial business impact.
Security Impact
Using this vulnerability, attackers without credentials or otherwise
legitimate access can exploit this weakness in Log4j to issue system-level
commands, corrupting, disabling, or taking over a system. Subverted systems can
then be used to deploy ransomware or attack protected, critical systems and exfiltrate sensitive data from organizations bypassing security controls.
Urgent Actions Required
Recommendations
Lightstream recommends operating a comprehensive vulnerability management program and prioritizing issues like Log4j vulnerabilities as business-critical fixes.
If your organization does not have a functional vulnerability management program, Lightstream can help – we operate full-stack vulnerability management programs for our customers, keeping you ahead of emerging threats and attackers.
Register for Lightstream Insights
©2024 Lightstream Managed Services, LLC. All Rights Reserved.